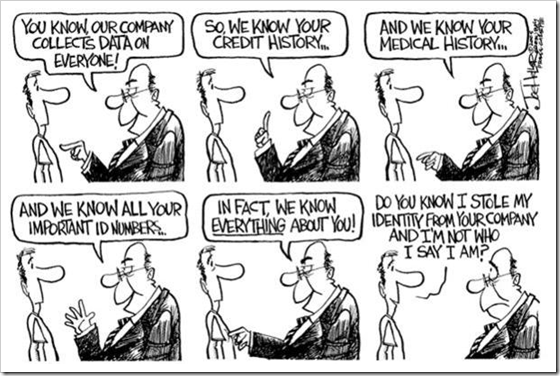
Being part of the honored 2% isn’t so gratifying

On April 4th, I received apology letters from my bank, a major retailer, a large pharmaceutical chain, and three hotel companies.  All of the apologies were similar, but I’ll share just one:
Dear Ritz-Carlton Customer,
We were recently notified by Epsilon, a marketing vendor The Ritz-Carlton Hotel Company uses to manage customer emails, that an unauthorized third party gained access to a number of their accounts including The Ritz-Carlton email list. We want to assure you that the only information obtained was your name and email address. Your account and any other personally identifiable information are not at risk.
Please visit our FAQ to learn more.
In all likelihood, this will not impact you. However, we recommend that you continue to be on the alert for spam emails requesting personal or sensitive information. Please understand and be assured that The Ritz-Carlton does not send emails requesting customers to verify personal information.
It must have really hurt Ritz Carlton, that paragon of sophistication and propriety, to fall on its virtual knees and send out thousands for such emails.
I subsequently learned that USA Today reported:
With the possible theft of millions of e-mail addresses from an advertising company, several large companies have started warning customers to expect fraudulent e-mails that try to coax account login information from them.
Perhaps the Wall Street Journal wanted to make me feel special, one of select few:
Alliance Data (parent of Epsilon) reiterated that social-security and credit-card numbers were not stolen. It also said that only 2% of its more than 2,500 customers were affected.
I have yet to know whether there will be a harmful personal affect from this data breach. But it does illustrate that we are all vulnerable, whenever we trust any confidential information to someone else.
Technorati Tags: Identity Theft, Information Security, Privacy