Thanks to Malisa Vincenti, leader of the LinkedIn Group Security & Technology – Critical Infrastructure Network & Forum, for highlighting the CNN article entitled “Why face recognition isn’t scary – yet.â€
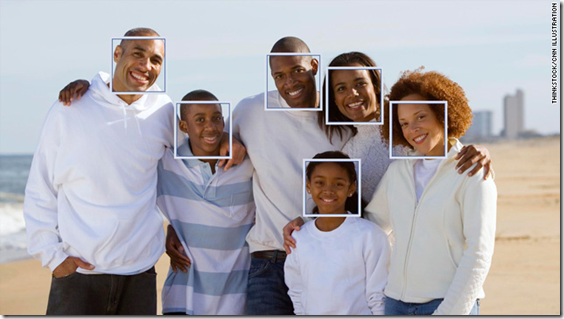
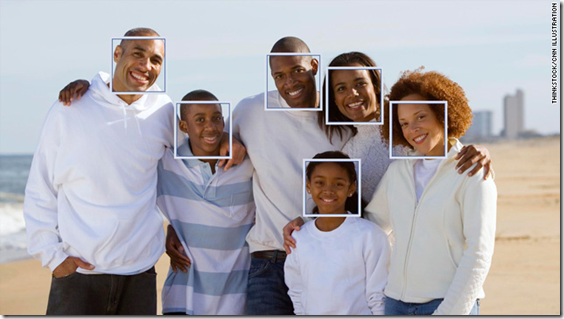
Much of the article was dedicated to describing the benefits and deficiencies of facial recognition software used by online services like Facebook, Picasa and iPhoto to make it easier for users to keep track of photographs. Speaking of such functionality, Michael Sipe, vice president of product development at Pittsburgh Pattern Recognition, a Carnegie Mellon University split-off company that makes face-recognizing software said these types of photo programs are a response to the hassles of keeping track of growing digital photo collections.
"In general, there’s this tsunami of visual information — images and video — and the tools that people have to make sense of all that information haven’t kept pace with the growth of the production of that information," he said. "What we have is a tool to help extract meaning from that information by using the most important part of that media, which is people."
It is interesting that one of the most distinguishing attribute of a person’s identity – his or her face – is so difficult for computers to recognize. We humans often say, “I can remember faces much better than names,†yet computers are just the opposite. It turns out that a person’s smile, which may be one of the most easily-remembered feature of the human face (for us humans, at least), is the most difficult for computers to comprehend:
Anil Jain, a distinguished professor of computer science at Michigan State University, said it’s still not easy, however, for computers to identify faces from photos — mostly because the photos people post to the internet are so diverse.
Computers get confused when a photo is too dark, if it’s taken from a weird angle, if the person is wearing a scarf, beard or glasses or if the person in the photo has aged significantly, he said.
Smiling can even be a problem.
"The face is like a deformable surface," he said. "When you smile, different parts of the face get affected differently. It’s not just like moving some object from one position to another," which would be easier for a computer to read.
So … what will happen when this technology matures and makes the leap from family-friendly Facebook to applications in real live security or survellance applications?
Marc Rotenberg, executive director of the Electronic Privacy Information Center, said the motives behind the technology are what worry him.
Governments and corporations intend to use facial recognition software to track the public and to eliminate privacy, he said, noting that automatically identifying people in public in the U.S., when they are not suspected of a crime, could be a violation of constitutional rights.
When facial recognition comes to surveillance cameras, which are already in place, "you’re no longer racing through iPhoto to figure out how many pictures of Barbara you have," Rotenberg said. "You’re walking around in public and facing cameras that know who you are. And I think that’s a little creepy."
I suppose this is like many other technologies – there are an abundance of positive applications, and the potential for terribly nefarious uses.
For example, if facial recognition can be used to identify terrorists so they could be detained prior to boarding airplanes, we would generally think that was a good application.
Similarly, if I could be granted entrance to my corporate office building or be logged onto necessary computer systems just by smiling (or frowning) into a camera, the building and computer systems might be more secure and the present-day use of passwords or ID cards might go the way of the buggy whip.
However, if an abusive husband used facial recognition software to stalk his estranged wife, or if the government successfully tracked every movement its citizens made in the normal course of events, we would generally think of those applications as negative.
I have a crazy habit of smiling and waving at security cameras I see in airports or banks or convenience stores. Who knows what is happening on the other side? At the present level of today’s technology, I’m probably being recorded and not much more. In a few years, however, the sophisticated software behind the camera will probably recognize Mark Dixon and report my antics to the NSA. That will surely make me frown, not smile, when I wave to the ubiquitous cameras.