Protecting the Electric Grid in a Dangerous World
 When I woke up this morning, I read an intriguing tweet from my son Eric, who lives about a mile away from our house:
When I woke up this morning, I read an intriguing tweet from my son Eric, who lives about a mile away from our house:
“Power has been out for 30 minutes. We have like 15 candles lit… And it’s starting to heat up.â€
Well, for young Eric and his wife, a temporary power outage might be a romantic diversion, but we are all tremendously dependent upon available, reliable electricity distribution. We simply expect the lights to go on when we flip a switch or power our laptops when we plug them in.
In order for that to happen, the national electrical grid or Bulk Electrical System (BES) must reliably carry energy from generating plants to our homes and places of business. We have grown to rely on that happening, 24x7x365.
However, according to a new white paper published by Oracle,
“there is mounting evidence that North America’s bulk power systems are dangerously exposed to threats from both within and abroad.â€
A few warning signs include:
- In June 2007, the Department of Homeland Security (DHS) leaked a video that showed how researchers launched a simulated attack that brought down a diesel electrical generator, leaving it coughing in a cloud of smoke, through a remote hack that was dubbed the Aurora vulnerability.
- In January 2008, a CIA analyst revealed that a number of cyber attacks had cut power to several cities outside the U.S.
- In May 2008, the Government Accountability Office (GAO) issued a scathing report on the number of security vulnerabilities at the Tennessee Valley Authority, the nation’s largest public power company.
- In April 2009, The Wall Street Journal reported, according to unnamed current and former national security officials, that Russian and Chinese attackers penetrated the U.S. power grid, installing malware that could potentially be used to disrupt delivery.
- In July 2009, NERC CSO Michael Assante told the House subcommittee on Emerging Threats, Cyber security, and Science and Technology, “Cyber threats to control systems are
In response to these and other conditions:
â€the federal government has responded to this threat with a set of security standards for protecting cyber assets that comprise the BES, and set an aggressive schedule for mandatory compliance, beginning in 2007, with all covered entities required to be in ‘audit compliance’ by June 2010. Non-compliance could cost power companies up to $1 million per day in penalties.
“The North American Energy Reliability Corporation (NERC) Critical Infrastructure Protection (CIP) cyber security standards, mandated through the approval of the Federal Energy Regulatory Commission (FERC), provide a broad, though not very prescriptive guide to implement a comprehensive cyber security program, stressing responsibility and accountability for protecting the organization’s critical assets.â€
 The new Oracle white white paper, entitled, “Protecting the Electric Grid in a Dangerous World,†describes how Oracle Identity Management solutions and the Oracle data security portfolio offer an effective, defense-in-depth security strategy to help meet this challenge, playing a key role in NERC CIP compliance, security and efficient use of resources.
The new Oracle white white paper, entitled, “Protecting the Electric Grid in a Dangerous World,†describes how Oracle Identity Management solutions and the Oracle data security portfolio offer an effective, defense-in-depth security strategy to help meet this challenge, playing a key role in NERC CIP compliance, security and efficient use of resources.
Identity Management:
“Oracle Access Manager, Oracle Identity Manager, Oracle Identity Analytics and other products in the suite of Oracle Identity Management solutions provides application and system-level security, giving power providers and distributors the tools to create sustainable, manageable and auditable controls over access to their critical assets. Identity management and access control are essential components in CIP-003, CIP-004, -005, -006, -007, and are applicable in -008, -009.â€
Data Security:
“Oracle’s comprehensive data security portfolio, including Oracle Advanced Security, Oracle Data Masking, Oracle Database Vault, Oracle Label Security and Oracle Audit Vault, allow managing critical information throughout the data protection lifecycle by providing transparent data encryption, masking, privileged user and multi-factor access control, as well as continuous monitoring of database activity. Database security, especially data access controls and privileged user management are essential in CIP–003, -004, -005, -006, -007, -008 and -009.â€
 It’s great to be a associated with a company whose products can play a major role in the protection of our electrical grid upon which we depend so much.
It’s great to be a associated with a company whose products can play a major role in the protection of our electrical grid upon which we depend so much.
However, I must admit, lighting a few candles after dark may be enjoyable as well!
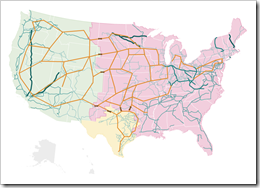
PS: The grid map shown above comes from an interesting interactive map on the NPR.org website. Enjoy!
