SquareTag Project Report
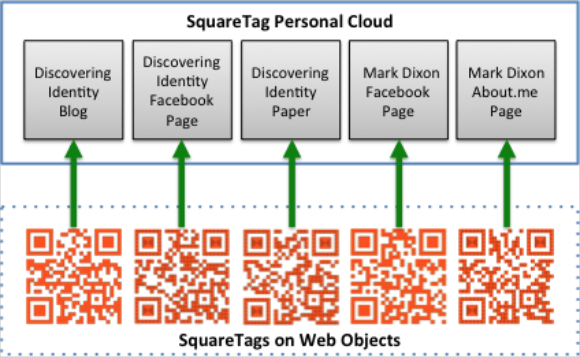
About two months ago, I started a small project to see how SquareTags would work on virtual objects like web pages. Subsequent posts are here, here, here and here.  This post summarized what I learned.  Thanks to Phil Windley and his team for encouragement and support.
One by one, I tagged a few web pages I control with a Square Tag and defined an object in my SquareTag personal cloud as illustrated below.
Â
I invited people to scan the tags and send me a Twitter ID or email address so I could respond. I received about 40 responses from nine states in the US, plus four other nations. Â Not bad for a little blog way out on the long tail of online information.
Here are some things I learned:
Tagging virtual objects works as well as physical objects (I tagged some physical stuff, too.)
I was able to easily link information in my personal cloud to the virtual objects. Â The personal cloud could potentially be a comprehensive repository for all my physical and virtual possessions.
In the cases of Facebook, About.me and Paper.li (the Discovering Identity Paper), the tags are embedded in a .jpg image, so the host site probably doesn’t even know the links exist.
Orange works just as good as black for SquareTags. Â I started by using photos of the adhesive SquareTags I purchased, but then created orange tags which encoded the SquareTag URL and code for each tag.
I don’t think QR Codes are broadly used by most people. Â I had to explain to several people I know what the codes were and explain what they needed to do to scan a SquareTag.
The user experience presented when someone scanned a SquareTag wasn’t optimized for this experiment. Â Only one field was available, so having people uniformly offer both a contact point (Twitter ID or email address) and location didn’t always work. Â Sometimes I would receive geo coordinates, but that required that a person opted in to use them.
All in all, it was an enjoyable experiment. Â I think I’ll leave the tags in place for awhile, just to see if anyone else responds. Â After all, I got one out of the blue yesterday.