Digital: “of, relating to, or using data in the form of numerical digits“
Transformation: “change in form, appearance, nature, or character.”
The more I read about and discuss the hot buzzword “Digital Transformation,†the more I think of the old “Blind Men and the Elephant†story.  Each blind man’s perception of reality was different, depending on which part of the elephant’s anatomy he examined. The meaning of Digital Transformation also seems to depend highly on who is thinking about the subject.
First, consider a few examples of how business leaders may think of Digital Transformation:
To the business leader who has the vision of leveraging a company’s vast data resources to open new revenue opportunities through selling access to that data to interested customers, Digital Transformation is all about rapidly delivering that digital asset (data) to customers in new, innovative ways.
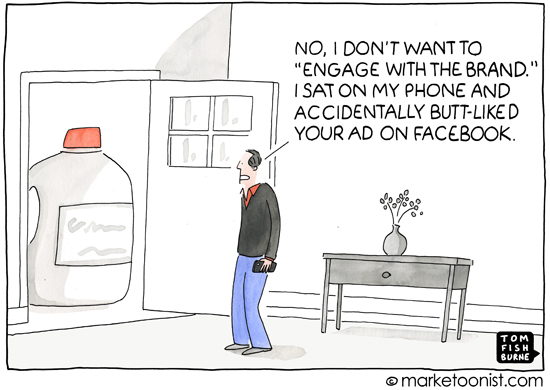
To the leader who is primarily interested in customer acquisition and loyalty in a consumer goods market, Digital Transformation may include “store of the future†concepts and providing a omni-channel customer buying experience.
To the health care executive, Digital Transformation may include providing electronic health records for patients that span multiple care providers to provide a more seamless and effective experience for patients and more profitable revenue channels for the many enterprises involved.
I’m sure thou can think of many more business examples.
Now think about what you have heard technology vendors say about Digital Transformation:
“You must leverage the Cloud to enable Digital Transformation.”
“Exposing and consuming APIs are essential are essential to Digital Transformation.”
“Digital Transformation is removing or consolidating information system silos.”
“Digital Transformation is all about enabling multi-channel customer experience.”
“Digital Transformation is all about harnessing Big Data.”
There are lots of body parts to the Digital Transformation elephant. Each of the viewpoints above is somewhat correct, but is lacking in completeness. Â Digital Transformation is a big subject.
Perhaps the overall business perspective might be described in these ways:
Digital business models have become essential for companies across a range of industries. … going digital is now a prerequisite for surviving and thriving. (McKinsey)
Competing successfully in the digital industrial economy is rapidly becoming a leading strategic imperative for businesses all around the world. (Gartner)
Digital Transformation involves dramatically changing the enterprise to embrace and leverage digital technology to compete in new, innovative and disruptive ways.
From the technology viewpoint, we must remember that technology must enable business, not just exist for the sheer beauty of new stuff. Many technologies are converging to enable Digital Transformation – Mobile, Social, Cloud, Big Data, Internet of Things, APIs – I have probably missed a few. Any or all of these technologies can be leveraged in a Digital Transformation, depending on what is needed to support the business. No single technology is sufficient. Â
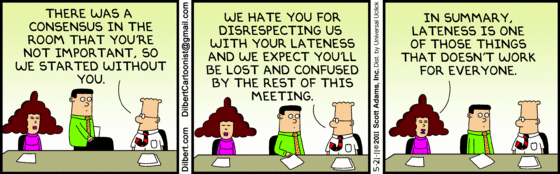
We must remember that huge changes must be made in IT to enable dramatic changes in business. Gartner’s Peter Sondergaard recommends:
Digital startups sit inside your organization, in your marketing department, in HR, in logistics and in sales. As IT leaders, you must design, resource and deploy for a world that’s digital first. In this new model, every business unit is a technology startup. Now is your opportunity to create that team. Partner with the digital startups inside your organization and prove that you can move fast too. Embrace the outside change.Â
Taking both business views and IT views into consideration, I rather like this definition of Digital Transformation from the Agile Elephant, a UK based consultancy:
Digital transformation is the process of shifting your organisation from a legacy approach to new ways of working and thinking using digital, social, mobile and emerging technologies.  It involves a change in leadership, different thinking, the encouragement of innovation and new business models, incorporating digitisation of assets and an increased use of technology to improve the experience of your organisation’s employees, customers, suppliers, partners and stakeholders.
This made me remember a statement made by Tom Peters in his book, Thriving on Chaos, which I first read in 1989:
Excellent firms don’t believe in excellence – only in constant improvement and constant change. That is, excellent firms of tomorrow will cherish impermanence and thrive on chaos!
A word of warning, however. Several years ago, when “Business Process Re-engineering” was a popular buzzword, a friend of mine was really excited when he was first assigned to a re-engineering team in his company.  He was not so happy a while later when he hold me his position in the company was re-engineered. He had been laid off!
We must be agile ourselves to survive and thrive!
Â




 My cyberspace friend
My cyberspace friend