Identity Trend 4: Identity Assurance
 This post is the fourth in a series of eleven posts I am writing about important trends in the Identity Management industry.
This post is the fourth in a series of eleven posts I am writing about important trends in the Identity Management industry.
When you present identity credentials to log into an enterprise system or online Internet site, are you really whom you claim to be? Do your credentials represent the “real you?â€
I published one of my favorite blog posts, entitled “OpenID Credibility: Harry and Bess Truman,†back in June, 2007. A brief excerpt:
I visited MyOpenID.com and was issued an identifier for Harry Truman: http://harrytruman.openid.com. No validation, no verification of Harry’s real Identity. I just plugged in President Harry Truman’s birthday and home town. I did use my own personal email address, but it wasn’t even validated at the time.
Armed with my new bogus identifier, I marched over to Jyte.com and made a couple of claims: The Buck Stops Here and I Love Bess.
Interestingly enough, the Jyte.com links still work!
This little exercise, where I wasn’t really THE Harry Truman, illustrates the need for Identity Assurance to validate whether my identity credentials really represents who I really am. Identity Assurance can be described as “a means to allow Identity Providers (IdPs), Relying Parties (RPs) and subscribers to determine the degree of certainty that the identity of an entity presenting an electronic identity credential is truly represented by the presented credential.â€
With the continual expansion of online fraud and other threats to online security and privacy, the need for Identity Assurance methods are rising. Being able to certify the that the correct Identity credentials are issue to the correct user before access is attempted is an increasingly critical issue.
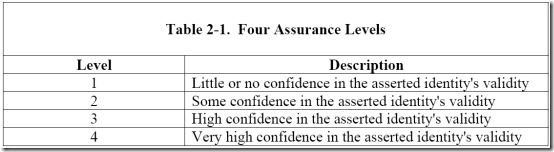
The Liberty Alliance Identity Assurance Framework defines four progressive levels of assurance, depending on confidence in the asserted identity’s validity, as shown in the following table from the Liberty Identity Assurance Framework document.
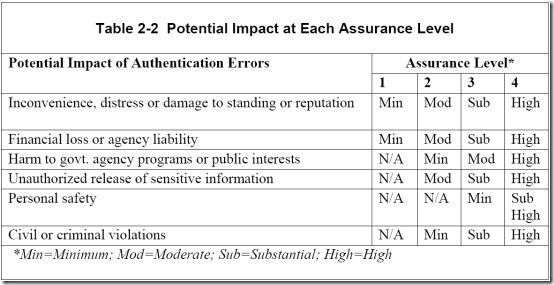
By comparing the assurance level against the potential impact of authentication errors, we get a clear picture of how the wide spectrum of online access transactions require substantially different levels of Identity assurance.
My impersonating the late Harry Truman requires minimal assurance because the potential impact for the transactions I conducted is minor. However, at the other end of the spectrum, identity credentials used to conduct high value financial transactions protected by civil or criminal statute are probably worthy of far more stringent Identity Assurance screening.
So, who is responsible to issue high level credentials? Should it be the government, who is responsible for issuing validated credentials like birth certificates, passports and drivers licenses? Should it be private enterprise? It depends on the two factors illustrated above: Assurance Level and Potential Impact.
Recommendations:
Consider these questions for your specific cases:
- What level of assurance do you require to match the risk (potential impact) to the cost and complexity of issuing identity credentials?
- What different levels may be appropriate for different applications or systems for which you are responsible?
- What sources of validation are appropriate to assure that the identity credentials you issue are valid?
- What should the role of government or private enterprise have in Identity assurance?
By the way, I still think Harry and Bess look good together. What do you think?

[Trackback] I had occasion recently to sit down to talk with Reliable Identities‘ Wes Kussmaul, accomplished entrepreneur, author, and prolific Internet tinkerer. Wes experienced early success founding the Delphi Internet service. (Some of the more seasone…
Mark, I have enjoyed this article very well, which means, I suppose that I shall have to catch up also with your other Trends. Is it just me, or is this discussion on identity authentication getting lost in the shuffle? I do not see ‘real-person’ identity authentication being seriously addressed? I have discussed this a bit on a blog posting today (http://nettingitout.com/2009/11/11/do-i-know-you-identity-authentication-in-the-real-and-digital-worlds/), and would enjoy your comments.
Robert:
Thanks for stopping by and sharing your insight – and for including a link to this blog in your blog post.
I think Identity authentication to which you refer can be discussed at at least two levels:
1. The authentication of identity credentials that happens when you log into on online service. This may be limited to user name/password or additional levels of "strong authentication", which may include security tokens, smart cards, biometrics or other means.
2. The "Identity Assurance" step, which must happen when the identity credentials are issued. This may require face-to-face verification of your identity, presentation of a birth certificate or some other method of verifying that you are the person you claim to me. This is the process of matching the "real person" identity with the credentials that will be used when you log on.
In my blog post above, my example of claiming to be Harry Truman is at one end the spectrum, where no Identity Assurance was performed. At the other end of the spectrum may be the issuing of Identity Credentials after an FBI background check has been performed. The level of Identity Assurance should match the level of risk that is appropriate for the situation.
Does this address your questions? I’d be happy to discuss further if that would help.
Thanks,
Mark
[Trackback] I had occasion recently to sit down to talk with Reliable Identities‘ Wes Kussmaul, accomplished entrepreneur, author, and prolific Internet tinkerer. Wes experienced early success founding the Delphi Internet service. (Some of the more seasone…