On Monday, the White House released a policy paper entitled, “A Policy Framework for the 2st Century Grid: Enabling Our Secure Energy Future.”  This report sets forth policy recommendations that build upon the Energy Independence and Security Act of 2007 and the Obama Administration’s smart grid investments to foster long-term investment, job growth, innovation, and help consumers save money.
On Monday, the White House released a policy paper entitled, “A Policy Framework for the 2st Century Grid: Enabling Our Secure Energy Future.”  This report sets forth policy recommendations that build upon the Energy Independence and Security Act of 2007 and the Obama Administration’s smart grid investments to foster long-term investment, job growth, innovation, and help consumers save money.
The document’s foreword states:
A smarter, modernized, and expanded grid will be pivotal to the United States’ world leadership in a clean energy future. This policy framework focuses on the deployment of information and communications technologies in the electricity sector As they are developed and deployed, these smart grid technologies and applications will bring new capabilities to utilities and their customers In tandem with the  development and deployment of high-capacity transmission lines, which is a topic beyond the scope  of this report, smart grid technologies will play an important role in supporting the increased use of  clean energy.
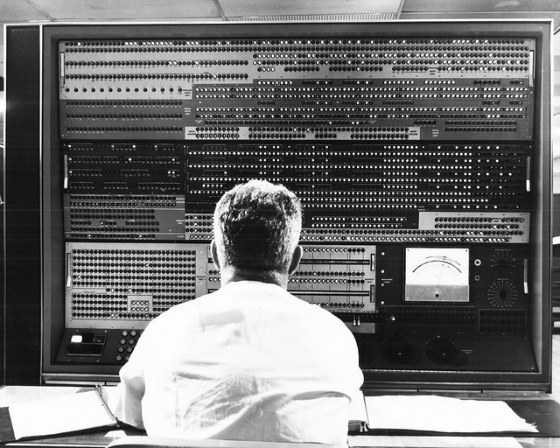
A 21st century clean energy economy demands a 21st century grid. Much of the traditional electricity  infrastructure has changed little from the original design and form of the electric grid as envisioned by Thomas Edison and George Westinghouse at the end of the 19th century (EEI 2011, p6). In a 21st  century grid, smart grid technologies will help integrate more variable renewable sources of electricity,  including both utility scale generation systems such as large wind turbines and distributed generation systems such as rooftop solar panels, in addition to facilitating the greater use of electric vehicles and  energy storage. Moreover, such technologies will help enable utilities to manage stresses on the grid, such as peak demand, and pass savings on to consumers as a result.
The report introduction explains further:
The Federal Government, building on the policy direction set forth in the Energy Independence and Security Act of 2007 and the Recovery Act’s historic investments in innovation, offers this policy framework to chart a path forward on the imperative to modernize the grid to take advantage of opportunities made possible by modern information, energy, and communications technology.
The report concludes:
Smart grid technologies and programs represent an evolution in how our electricity system operates. As this report highlights, this transition offers significant promise for utilities, innovators, consumers,and society at large. This document has outlined four essential pillars that will enable the United Statesto transition to a smarter grid:
- Enable Cost-Effective Smart Grid Investments: Smart grid technology can drive improvements in system efficiency, resiliency, and reliability, and help enable a clean energy economy through cost-effective grid investments. Many of these technologies promise to pay for themselves in operational improvements, and energy savings. The Federal Government’s research,development and demonstration projects, technical assistance, information sharing on technologies and programs, and evaluations provide valuable guidance for utilities, consumers, and regulators about what approaches are the most cost-effective, thereby paving the way for theeffective, ongoing upgrade of the grid.
- Unlock the Potential of Innovation in the Electricity Sector: A modernized electric grid promises to be a powerful platform for new products and services that improve grid operations and deliver comfort, convenience, and savings to energy customers.
- Empower Consumers and Enable Informed Decision Making: The success of smart grid technologies and applications depends on engaging and empowering both residential and small business consumers. New tools and programs promise to provide consumers personalized information and equip them to make informed energy choices, while ensuring their energyconsumption data is accorded privacy protections.
- Secure the Grid: Protecting the electric system from cyber attacks and ensuring it can recover when attacked is vital to national security and prosperity. Developing and maintaining threat awareness and rigorous cybersecurity guidelines and standards are keys to a more secure grid.
The current electric grid and the proposed smart grid are fascinating to me.  From my perspectives as a residential customer, a security professional and an old electrical engineer, it seems incredible that the old system we have works so well. At the same time, the emerging smart grid system should  have great benefits for us all … and provide huge employment opportunities to those involved for many years to come.