![Cyberdefense [article image]](http://cacm.acm.org/system/assets/0000/3587/081310.cnet.cyberdefense.large.jpg?1281708557&1281708557) CNET published a thought-provoking article last week, about Stuxnet, a sophiscated software worm that “targets critical infrastructure companies.†It “doesn’t just steal data, it leaves a back door that could be used to remotely and secretly control plant operations.â€
CNET published a thought-provoking article last week, about Stuxnet, a sophiscated software worm that “targets critical infrastructure companies.†It “doesn’t just steal data, it leaves a back door that could be used to remotely and secretly control plant operations.â€
This complex software is targeted not at desktop or laptop PC’s, but at industrial control systems. It has infected systems particularly in Iran and India, but also companies in the US.
The malware, which made headlines in July, is written to steal code and design projects from databases inside systems found to be running Siemens Simatic WinCC software used to control systems such as industrial manufacturing and utilities. The Stuxnet software also has been found to upload its own encrypted code to the Programmable Logic Controllers (PLCs) that control the automation of industrial processes and which are accessed by Windows PCs. …
An attacker could use the back door to remotely do any number of things on the computer, like download files, execute processes, and delete files, but an attacker could also conceivably interfere with critical operations of a plant to do things like close valves and shut off output systems
The eCommerce Times commented:
“The Stuxnet worm, which targets industrial control systems, or "SCADA" systems, is one of the most sophisticated bits of digital malware security researchers have come across in a long time. Now, those researchers want to know where it came from. Was Stuxnet the product of a den of hackers working on their own accord, or did a national government somewhere in the world have a hand in its creation?
"Given the sophistication and organization behind it, we highly suspect it has nation-state involvement rather than being a tool for competitive intelligence," Roel Schouwenberg, a senior antivirus researcher with Kaspersky Lab, told TechNewsWorld.
In a recent post, I quoted a report entitled, “21 Steps to Improve Cyber Security of SCADA Networks,†where the US Department of Energy stressed the importance of security in control systems:
The U.S. energy sector operates the most robust and reliable energy infrastructure in the world. This level of reliability is made possible by the extensive use of Supervisory Control and Data Acquisition (SCADA), Distributed Control System (DCS), and other control systems that enable automated control of energy production and distribution. These systems integrate a variety of distributed electronic devices and networks to help monitor and control energy flows in the electric grid and oil and gas infrastructure.
Automated control has helped to improve the productivity, flexibility, and reliability of energy systems. However, energy control systems communicate with a multitude of physically dispersed devices and various information systems that can expose energy systems to malicious cyber attacks. A successful cyber attack could compromise control systems and disrupt energy networks and the critical sectors that depend on them.
Securing control systems is a key element in protecting the Nation’s energy infrastructure. The National Research Council identified "protecting energy distribution services by improving the security of SCADA systems" as one of the 14 most important technical initiatives for making the nation safer across all critical infrastructures.
By targeting systems that control vital parts of a nation’s critical infrastructure, this worm is an example of how increasingly sophisticated technology can be used as an offensive weapon. Lots of questions still exist about this specific worm, but it really illustrates how we must be concerned about the security of all computer-based systems, not just those in data centers.
Somehow, this causes more concern in my paranoid mind than vulnerabilities in my iPhone.
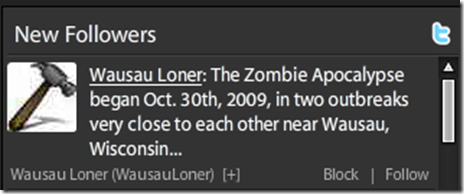
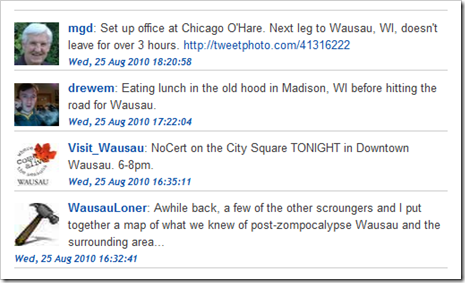
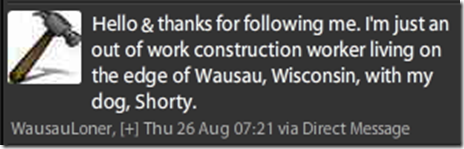
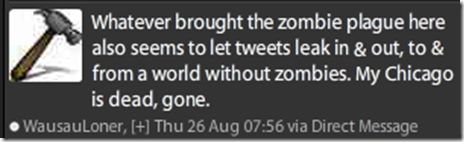
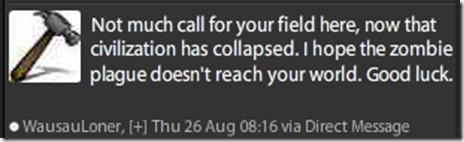 Well, there are still many unanswered questions. May be next time I visit Wausau, I’ll get together with Wausau Loner and get more details! I’ll let you know.
Well, there are still many unanswered questions. May be next time I visit Wausau, I’ll get together with Wausau Loner and get more details! I’ll let you know.

![Cyberdefense [article image]](http://cacm.acm.org/system/assets/0000/3587/081310.cnet.cyberdefense.large.jpg?1281708557&1281708557)