Identity Trend 10: Internet Identity
This post is the tenth in a series of eleven posts I am writing about key trends in the Identity Management industry.
 Much of the traditional Identity Management market grew up meeting needs of Identity Management for enterprises, but, of course, Identity plays a large, essential role in the external Internet as well. Modern enterprises are increasingly interconnected using the external Internet, but usually when we speak of Internet Identity, we are discussing the relationships between individuals and online service providers, as opposed to users of internal enterprise systems. In this context, at least two major characteristics of Internet Identity Management are substantially different than Enterprise Identity Management.
Much of the traditional Identity Management market grew up meeting needs of Identity Management for enterprises, but, of course, Identity plays a large, essential role in the external Internet as well. Modern enterprises are increasingly interconnected using the external Internet, but usually when we speak of Internet Identity, we are discussing the relationships between individuals and online service providers, as opposed to users of internal enterprise systems. In this context, at least two major characteristics of Internet Identity Management are substantially different than Enterprise Identity Management.
- Super-scale. Internet Identity systems must scale to accommodate hundreds of millions or billions of individual Identities, as opposed to hundreds of thousands in the largest enterprise Identity systems. Internet scale is enormous. Billions of people in the world have online accounts, and most online users have several online accounts, often across multiple devices. The administration of these enormous quantities of identity credentials is currently highly redundant, error prone and costly. Yet demands for privacy and security impose high standards on these Identity systems.
- User-managed Identities. Rather than supporting the typical “assignment†and “administration†of identity credentials in enterprise setting, Internet Identity systems typically allow users to “choose†and “manage†their own identity credentials. Ubiquitous standard methods do not yet exist to allow a common set of Identity credentials, managed by individual users, to be used with multiple online service providers. The current default method is for each service provider to act as its own “Identity Provider†as well as being a “Service Provider†or “Relying party†that accepts a standard credential. For example, Google, Yahoo, Facebook and Amazon.com each operates its own Identity Provider function without allowing a user to use a common set of identity credentials across all these major service providers. While technical standards exist to enable a common Identity Provider serving multiple relying parties, we have not yet seen broad acceptance of an Identity Provider / Relying Party Identity infrastructure.
Multiple companies such as Facebook, Google, Yahoo, PayPal and Equifax have expressed interest in becoming Identity Providers for the Internet. Certainly they have demonstrated the ability to provide highly performant systems at Internet scale. Some relying parties have begun to demonstrate acceptance of Identity credentials from such Identity Providers, but clear winners haven’t yet emerged. For example, Facebook and Google both provide facilities for other online sites to accept their Identity credentials, but uptake by relying parties has been fairly limited so far.
The biggest obstacles slowing widespread acceptance seem to be:
- Business Model. Lack of a clear financial business model to support the separation of Identity Providers from relying parties. It is yet unclear what financial compensation should be provided to an Identity Provider by a Relying Party. What business model is financially sustainable?
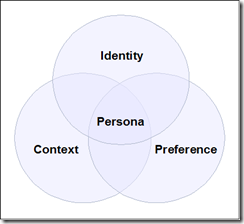
- User Control. The desire of big service providers to maintain exclusive control over their own user base. Online service providers recognize that huge value is inherent in a large user base, particularly when combined with usage data that can be mined to provide context and preference information as discussed in my recent blog post.
- Ease-of-use vs. Security. Tension that exists between the need for a secure Identity credential system and the need for extreme ease-of-use by online users. Some methods, such as Infocard/Cardspace and OpenID, have definite ease-of-use advantages over traditional systems, but serious concerns exist about whether either system can support high levels of security or Identity Assurance.
An example of cooperative efforts to address these challenges is the US Government Open Identity Initiative, which seeks to leverage existing industry credentials for Federal use of Internet Access. Trust frameworks from organizations such as the Kantara Initiative, OpenID Foundation, InfoCard Foundation and InCommon Federation are being considered. Google, Yahoo, Paypal and Wave are participating in this project as Identity Providers. While the current focus is on enabling Infocard/Cardspace and OpenID for low-security access to government websites, concern has been expressed that neither method would be sufficient for higher security needs.
Recommendations:
The following questions may be in order as you consider how your organization will address Internet Identity:
- How many online users do you have now?
- How fast are you growing?
- What specific security and privacy assurance levels must you provide?
- How could easy-to-use, yet highly secure Identity credentials help you and your users?
- Will you be willing to rely on a third party Identity Provider to authenticate users to your site?
- What control do you want to entrust to your users to manage their own Identities?